We offer complex services: from business analysis to designing, implementing, integrating, testing, and maintaining systems. We expand existing systems and create original solutions.
What are our areas of expertise?
- Network Asset Management
- Field Service Management
- Collecting, integrating, and processing data, also using artificial intelligence and machine learning (AI/ML)
- Map-based solutions
- Solutions for the renewable energy industry (RES)
We also provide services related to system analysis, integration, and audit. We take commissions for custom solutions. Our specialists can use their skills to support your team as well.

Specialized applications
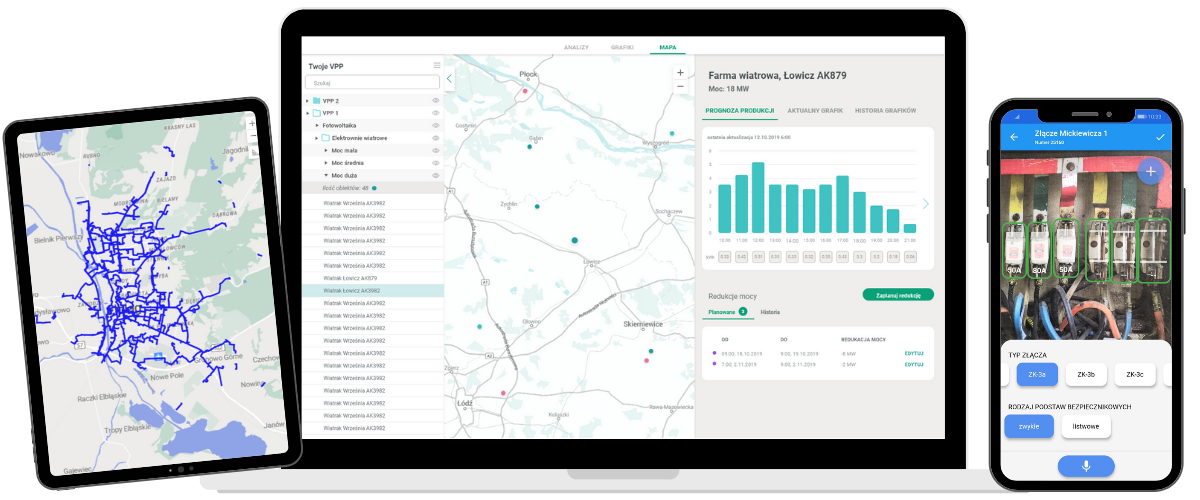
Our team creates specialized geospatial solutions for business. We design and build:
- advanced industry applications (desktop, web, and mobile) for telecommunications, district heating, energy (including renewables), and others
- high-quality OSS/BSS tools and inventory/asset management systems
- FSM (Field Service Management) and MWFM (Mobile Workforce Management) solutions for managing mobile work and employees
- business analysis tools based on artificial intelligence algorithms
We are a Google Premier Partner and specialize in Google Maps. We create scalable, reliable solutions that improve business effectiveness based on Google Maps and Google Cloud platform products.
System integrations
We integrate our solutions with customers’ IT architectures including CRM, ERP, billing, accounting, technical, and workflow systems.
We use tools such as GE GeoSpatial Server and SAP Business Interface. We have experience integrating on SAP and NetWeaver platforms.
The highest software development standards
During our software development process, we rely on the best practices related to agile methods such as SCRUM. Our project managers own Prince 2 certificates.
Our work is based on the newest technologies and tools from our market-leading partners.
Top security of software and data
We place special emphasis on the security of our solutions and the protection of our customers’ data. We follow security recommendations and best practices derived from ISO 27001, NIST, and other standards.
In the software development process, solutions are tested according to the OWASP TOP10 and OWASP ASVS methodologies. We use static code analysis, vulnerability verification of images and of third-party components.
We adhere to a strict separation between development and production environments, to which only solution administrators have access.
Administrative access is protected by two-step verification, with phishing-resistant authentication methods.
We use full separation of the data of each of our clients, which prevents accidental access by unauthorized individuals from another organization.
Technologies we use
Our experience
Since 1997 we completed hundreds of programming projects, both small and large. Our solutions support over 700 customers around the world.
Let’s talk!
Would you like to use our services? Fill out the form and our consultant will reach out to discuss your needs and the next steps.
22 848 73 13
sales@globema.pl